As we get into the summer, many business owners and employees look forward to a well-deserved break. However, high achievers are known to do a little work on vacation. Unfortunately, studies show that working outside the office, whether on vacation, from a local coffee shop, or even business travelers out on work trips, can lead to significant cyber security issues. If you or your employees plan on answering urgent emails or checking in on projects while on vacation this summer, it’s essential to maintain strong cyber security best practices to avoid exposing the company network to hackers preying nearby. In this blog post, we’ll cover what cyber security best practices for remote workers must be implemented so that you and your team can get your work done and enjoy your vacation without worrying about a data breach.
Why Cyber Security Matters While Traveling
For business travelers, the need to stay connected to the office is a reality of the digital age, and our handheld devices make it easy. But with this constant connectivity comes an increased risk of cyber threats. Whether you’re using a public Wi-Fi network in the lobby or accessing sensitive files from your hotel room, you can expose your company to hackers, malware, and other cyber risks.
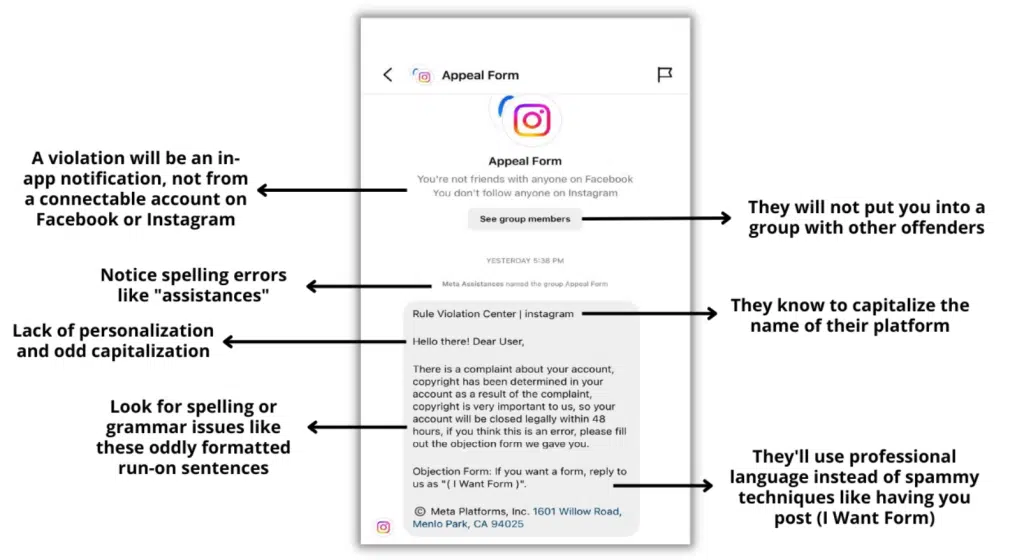
Cybercriminals know how this works! They understand that people are more likely to let their guard down while on vacation. They know you’re more focused on enjoying your time off than ensuring your devices are secure. This situation makes travelers an attractive target for cybercriminals, who can use a variety of tactics to compromise your data, such as phishing emails, fake websites, and man-in-the-middle attacks.
To minimize the risk of a cyberattack while traveling, here are a few best practices to cover with your team:
- Use A Virtual Private Network (VPN): A VPN encrypts your internet connection, ensuring your data is secure even when using public Wi-Fi networks. Before you leave, set up a VPN on your devices and use it whenever you’re online.
- Keep Your Devices Updated: Before leaving for vacation, update your devices to the latest software and security patches. Outdated software can leave you vulnerable to cyberattacks, so staying current is essential.
- Be Wary Of Public Wi-Fi: Although convenient, public Wi-Fi networks can be a hotbed for cybercriminal activity. Avoid using these networks whenever possible. Yes, that means no checking your email poolside unless you have a VPN.
- Enable Two-Factor Authentication (2FA): Using 2FA adds an extra layer of security to your accounts by requiring a second form of verification, such as a text message code or fingerprint scan. Make sure to enable 2FA for all of your critical accounts before you depart.
- Beware Of Phishing Attempts: Cybercriminals often target travelers with phishing emails, which are designed to trick you into revealing sensitive information. Be cautious of any emails you receive while on vacation, and never click on suspicious links or download unfamiliar attachments.
- Secure Your Devices: Physically secure your devices by always keeping them with you and never leaving them unattended in public places. Additionally, enable password protection, biometric authentication when applicable, and remote wiping capabilities in case your device is lost or stolen.
Traveling for business or pleasure doesn’t mean you should compromise on cyber security. Following these best practices can reduce the risk of a data breach or other cyber security issue while away from the office. However, it’s important to know that these steps aren’t infallible. To truly ensure that your company’s cyber security measures are up to par, you need to work with a qualified IT team that can monitor your network 24/7, patch any vulnerabilities that pop up (which happen regularly), and can alert you if something goes wrong.
To help you prepare for your vacation and have peace of mind knowing your business is secure while you or your employees are working remotely, click here to schedule a free IT assessment with our experts today. We’ll evaluate your current cybersecurity measures, identify potential vulnerabilities, and help you implement a strategic security plan to keep your company safe.