The holiday season is in full swing, which means so are the cybercriminals! While you’re making holiday gift lists, they’re plotting and scheming new ways to take advantage of unsuspecting online shoppers. Holiday phishing scams have become an all-too-common threat, targeting customers to steal personal information, financial data and even identities.
To help reduce the chances that a cybercriminal will ruin your much-deserved holiday fun, we’ve outlined a few of the most common and dangerous scams that you should be on the lookout for, how they work and tips to help you avoid becoming their next victim.
Understanding Holiday Phishing Scams:
Phishing is a deceptive technique cybercriminals use to trick individuals into sharing sensitive information such as passwords, credit card details or Social Security numbers. During the holiday season, these scams often take on a festive disguise, tricking victims with holiday-themed e-mails, messages and websites. Whether you’re ordering gifts for clients or friends and family, here are some common tactics used by holiday phishing scammers to be aware of:
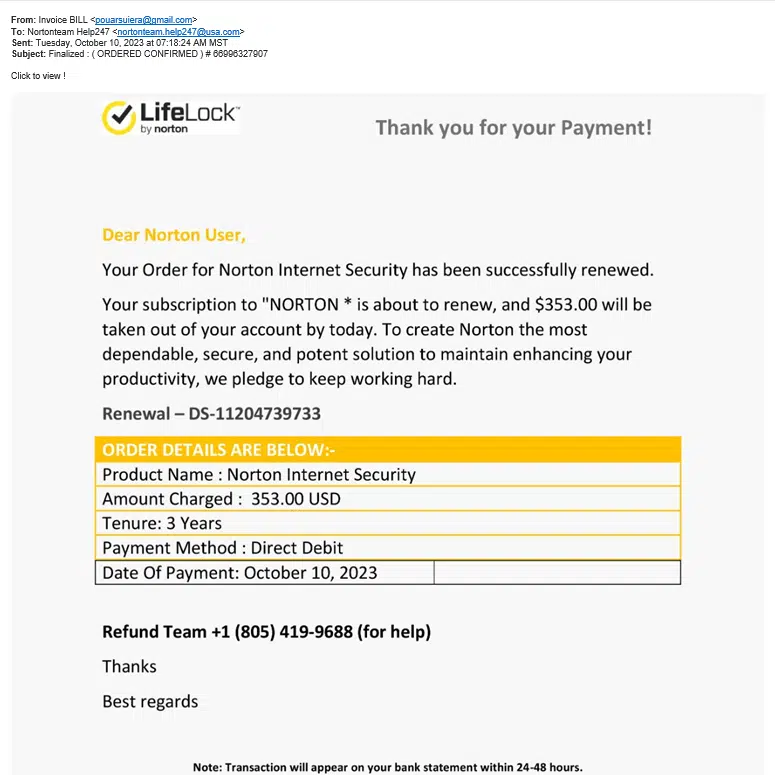
- Holiday-Themed E-mails: Scammers send e-mails that appear to be from trusted sources like your favorite retailers or even beloved charities. These e-mails look legit and usually offer fake exclusive holiday deals, order confirmations or requests for donations. Inside the e-mail, there is usually a link that leads to a fake website designed to steal your information or your money, or even install dangerous malware on your computer.
- Fake Promotions: Cybercriminals create fake holiday promotions and discounts that seem too good to be true. Unsuspecting victims see a great deal from a spoof e-mail account and are enticed to click on links or download attachments that can contain malware or lead to phishing websites.
Sometimes cybercriminals aren’t looking to install malware but instead hoping to steal your money. They’ll duplicate popular retailer websites or set up their own, so when you make a purchase, they’ll collect the money, but you’ll never receive your order. These sites are often difficult to track, making it hard to get your money back. - Delivery Notifications: With the increase in online shopping during the holidays, scammers send fake delivery notifications, claiming that a package is on its way or that there’s a problem with an order. These e-mails may prompt recipients to click on links or download attachments containing malicious software.
- Social Engineering: Scammers may impersonate friends or family members via e-mail or social media, asking for money or personal information under the guise of a holiday emergency or gift exchange. This is a common scam against seniors – who might not realize that the profile requesting money from them that was made “three days ago” isn’t actually their granddaughter – and young teenagers who don’t know fake profiles are an issue.
Recognizing and Avoiding Holiday Phishing Scams:
Now that we understand how holiday phishing scams operate, it’s essential to know how to recognize and avoid falling victim to them.
- Verify The Sender: Always check the sender’s e-mail address or domain. Be cautious of misspelled or suspicious e-mail addresses. Legitimate companies and organizations use official domains for their communication.
- Don’t Click On Suspicious Links: Hover your mouse over links to see the actual URL they lead to. Be wary of shortened links or URLs that don’t match the sender’s domain. If in doubt, visit the website directly by typing the URL into your browser.
- Beware Of Urgency And Pressure: Scammers often create a sense of urgency, claiming limited-time offers or imminent problems. Take your time to verify the authenticity of any claims before taking action.
- Double-Check Websites: Before entering personal or financial information on a website, ensure it’s secure. Look for “https://” in the URL, a padlock icon in the address bar and a valid SSL certificate.
- Use Two-Factor Authentication (2FA): Enable 2FA wherever possible, especially for online shopping and banking accounts. This provides an extra layer of security, even if your password is compromised.
- Educate Yourself And Others: Stay informed about current phishing tactics and share this knowledge with friends and family. The more people are aware, the harder it becomes for scammers to succeed.
- Protect Personal Information: Avoid sharing sensitive information via e-mail or text messages, even if the request seems legitimate. Use secure channels for such communication.
While the holiday season is a time for celebration and togetherness, it’s crucial to remain vigilant against holiday phishing scams. Cybercriminals prey on the festive spirit and increased online activity during this time. By recognizing the signs of phishing attempts and following best practices for online security, you can protect yourself and ensure a safe and joyous holiday season for you and your loved ones.
Business owners: If your staff will be ordering gifts online for clients, make sure they know how to spot a phishing attack and that your network is properly secured in case something slips through the cracks. You don’t want your organization to be negatively impacted by extending holiday goodwill. If you aren’t sure if you’re protected, please give us a call or schedule a 10-minute discovery session with our team. We can help give you peace of mind this holiday season. Click here to book now, and happy holidays!