Modern computers play a crucial role in various industries and in facilitating automation. But as technology continues to advance, so does the threat of computer viruses. And as the world goes digital, a virus is becoming too alarming to ignore.
A computer virus is a malicious software program that hijacks people’s personal stuff – like your data, identity, your accounts, and even your money. They can come in different forms, but their primary purpose is simple – to cause you and your computer harm. Its consequences can be severe. So it’s necessary to exercise due diligence when detecting one.
In this article, you can learn some common signs your computer is infected. Let’s dive in and learn how to detect a computer virus before it’s too late.
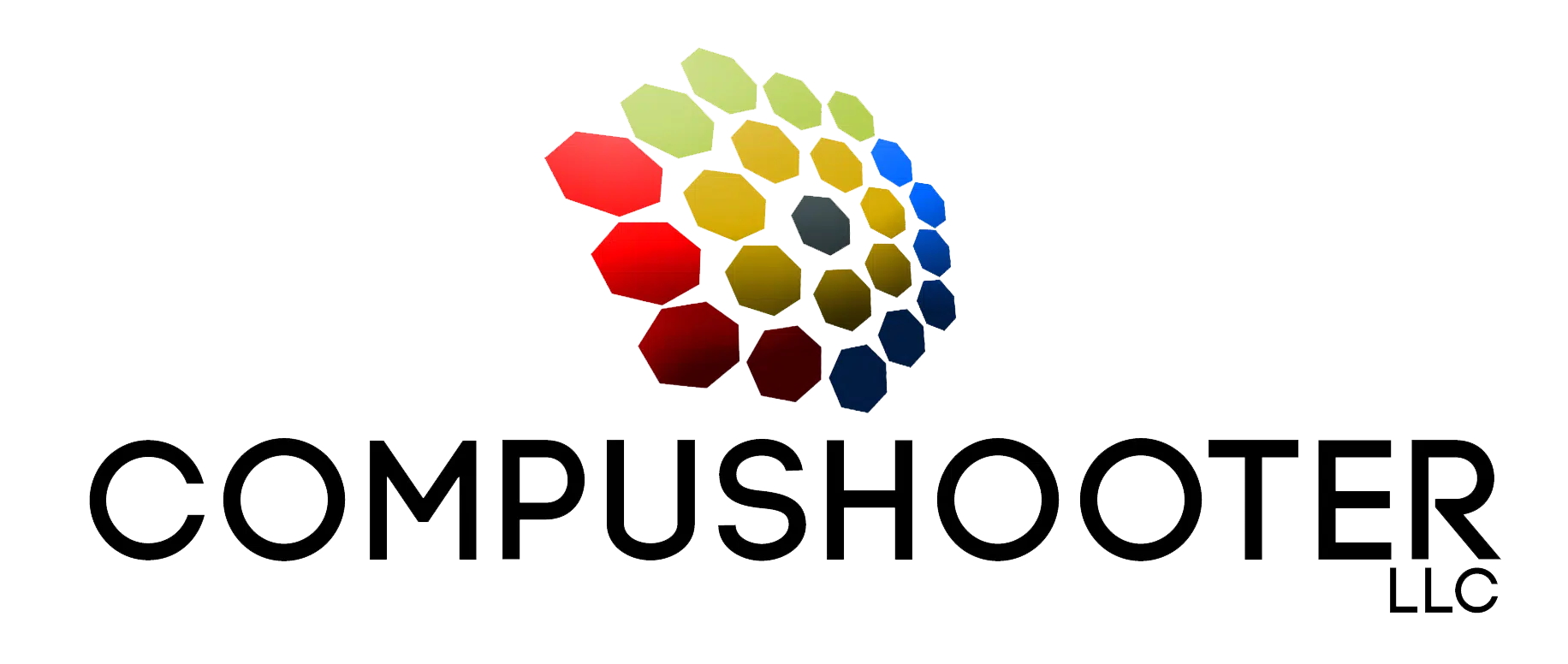
Common Signs of a Computer Virus
A computer virus can go from just infecting files to infecting the entire system. If you notice any of these signs, try running for an antivirus scam to check for potential damages to your computer.
Slowdown in system speed
A slow computer performance doesn’t automatically mean your computer has a virus. But it can be a red flag if it’s taking forever to open programs or load files – as the malware takes up your computer’s processing power. So if the lag is too noticeable and you’re struggling with even the simple tasks, it might be time to increase your cybersecurity measures.
Unwanted pop-up messages
Random pop-up messages that you didn’t ask for are the most accurate signs of a computer virus. Most messages can consist of warnings from fake antivirus software or requests for money. Its job is to grab your attention and invade your peaceful computer experience.
Frequent system crashes
Viruses can cause a computer to have a mind of its own. If your computer often crashes unexpectedly, then chances are viruses are interfering with your computer’s normal functions. The worst situation is that when you turn it back on, the virus has already destroyed all your files and made alterations to your computer.
However, not all viruses are designed to make your computer crash. So keep an eye out as some might just be lurking behind your computer files to avoid detection.
Missing files
A malware is well capable of corrupting and deleting data on your computer. And it doesn’t discriminate – it can delete anything from important documents to critical system files and damage your computer’s function. Severe ones are more contagious and spread the virus to other computers through emails.
Emails sent from your account
Cybercriminals often hijack infected computers to spread phishing schemes. If your friends are asking about suspicious links or strange attachments you supposedly sent, it’s a big red flag alert that a cybercriminal is working behind the scenes. These emails are phishing schemes used to spread malware or cause fraud.
Restore Your Computer’s Health
A computer virus mimics a real virus and spreads its influence to the entire brain of your computer’s system. Other viruses can be harmless and unauthorized access might just be as lucky as you can get, but untreated infections like these can extend to severe damages like financial losses.
If your computer is infected with a virus, the best move is to act promptly and seek help from an expert IT service provider. We can help you return your computer’s health to normal. Our team offers virus and malware removal services. Click here for a FREE 10-minute discovery call and we’ll discuss how we can help you.