Is your company looking to hire an IT firm? Unfortunately, unless you’re tech-savvy or experienced with IT contracts, there can be hidden costs that you wouldn’t expect or know to look for. While it can sound appealing to go for the cheapest firm, that decision can end up costing you more in the long run due to carve-outs and hidden fees in the contract. Cheaper IT firms will omit certain services from the original agreement and later nickel-and-dime you to add them on or by quoting you inadequate solutions that you’ll later need to pay to upgrade.
To help you weed out these companies that are not the bargains they advertise themselves to be, there are a few key elements to consider determining if your quote is insufficient, overpriced or underquoted.
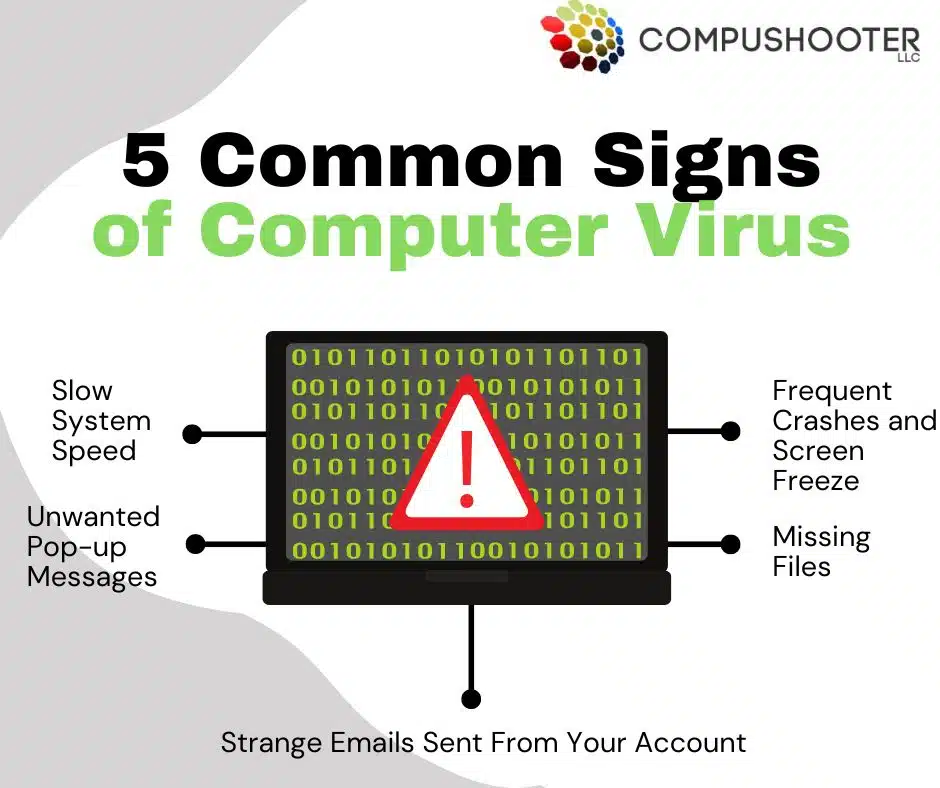
Insufficient Compliance And Cybersecurity Protections:
A ransomware attack is a significant and devastating event for any business; therefore, it’s imperative that the IT company you’re working with isn’t just putting basic (cheap) antivirus software on your network and calling it a day. This is by far the one critical area most “cheaper” MSPs leave out.
Antivirus is good to have but woefully insufficient to protect you from serious threats. In fact, insurance companies are now requiring advanced cyber protections such as employee cyber awareness training, 2FA (2-factor authentication), and what’s called “advanced endpoint protection” just to get insurance coverage for cyber liability and crime insurance. We provide those standards in our offering, so not only do you greatly reduce your chances of a cyber-attack, but you also avoid being denied an important insurance claim (or denied coverage, period).
Inadequate Recovery Solutions:
One thing you also want to make sure you look for in your IT firm proposal is that they do daily backups of your servers and workstations, as well as any cloud applications your company uses (Microsoft 365, Google Workspace, etc.), because online applications do NOT guarantee to back up your data. You also need to make sure your backups are immutable or unable to be corrupted by hackers. Again, most insurance companies now require immutable backups to be in place before they’ll insure against ransomware or similar cyber events.
Transparency About On-Site And After-Hours Fees:
This might take you by surprise, but most IT firms will charge EXTRA for any on-site or after-hours visits. We include ALL of this in our agreements, but ‘cheaper’ MSPs will intentionally leave this out and add it on later to make the sticker price appear lower. Make sure you understand what is and isn’t included in your service agreement before signing.
Nonexistent Vendor Liaison And Support:
Will they help you with all of your tech, or just select pieces that they’ve installed? Some IT firms will charge you hourly to resolve tech support issues with your phone system, ISP, security cameras, printers and other devices they didn’t sell you but that still reside on the network (and give you technical problems). These fees can stack up over time. As a client of ours, you get all of that INCLUDED, without extra charges.
Cheap, Inexperienced Techs And No Dedicated Account Managers:
One way some companies cut costs is by skimping on customer support and expertise. Many of the smaller MSPs will hire technicians under a 1099 agreement or find cheaper, less experienced engineers to work on your network and systems. The more experienced and knowledgeable a tech is on networking and, more specifically, cybersecurity, the more expensive they are.
Further, many smaller MSPs can’t afford dedicated account managers, which means you’re depending on the owner of the company (who’s EXTREMELY busy) to pay attention to your account and to look for problems brewing, critical updates that need to happen, upgrades and budgeting you need.
Good account management includes creating and managing an IT budget, a custom road map for your business and reviewing regulatory compliance and security on a routine basis to make sure nothing is overlooked. You get what you pay for, and this is NOT an area you want overlooked.
BEFORE you sign on the dotted line, it’s important to make sure that you fully understand what IS and ISN’T included in the service you are signing up for. It’s VERY easy for one IT services provider to appear far less expensive than another UNTIL you look closely at what you are getting.
If you’d like to see what dependable, quality IT support looks like, book a call with our team, and we’ll be happy to give you a quote that covers everything you need. To Schedule Your FREE Assessment, please visit https://www.compushooter.com/ or call our office at 602-691-2088