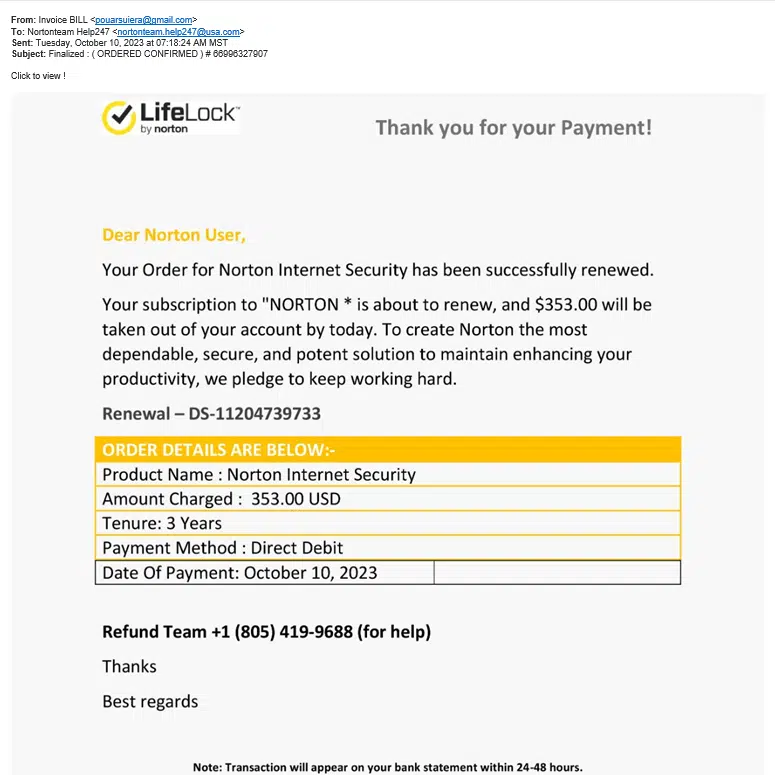
The Norton LifeLock Email Scam Unveiled
In today’s digital age, our personal information is more vulnerable than ever. Cybercriminals are constantly devising new and sophisticated methods to exploit unsuspecting individuals. One such threat is the Norton LifeLock email scam, a deceptive scheme that targets its victims with the promise of renewing your security while actually compromising information and safety. See sample image below.
The Norton LifeLock email scam operates under the guise of a you as a user renewing your subscription to their service, leveraging the trusted reputation of the Norton brand. Victims receive emails claiming to be from Norton LifeLock, stating that your Norton Internet Security has been successful renewed for a certain amount.
The scam normally preys on the account holders fear that their account had already been charged. Yes, these emails often contain urgent language, playing on fears of a large chunk of money has been charged on their account thus coercing recipients into taking immediate action. If you got really got charged with $353, you would certainly have it disputed with Norton as who they claim to be. Whoever you end up talking on the phone with you, they would try their best to get as much information from you to try to get the money for real.
Lo and behold, the alleged Refund Team is not Norton’s phone number. It is the number of the people scamming you.
Recognizing the signs of a email scam is crucial for protecting yourself and your personal information:
- Unsolicited Emails: Be wary of emails you didn’t expect or didn’t sign up for, especially those requesting personal information, payments, refunds or immediate action.
- Spelling and Grammar Errors: Scammers often make mistakes in language that a legitimate company would not. Pay attention to typos, awkward phrasing, or inconsistent formatting.
- Urgency and Pressure Tactics: Scammers often create a sense of urgency to pressure victims into making hasty decisions. Be cautious of emails that demand immediate action.
- Suspicious Links or Attachments: Avoid clicking on links or downloading attachments from unfamiliar sources. Hover over links to view the actual URL before clicking. (some scam campaigns variants do not include website links or attachments)
- Check the Sender’s Email Address: Verify that the email address matches the official domain of Norton LifeLock. Scammers often use slightly altered domain names to deceive recipients.
Always be Cautious with Personal Information: Avoid sharing sensitive information via phone, email or on unsecured websites. Legitimate companies typically request such information through secure channels.
These email scams get recycled and updated to suit the scammers needs, today it is Norton, tomorrow they might pretend to be Bank of America, Chase, FedEx, DHL, PayPal or something else.